Demo Overview
The tutorial provides a how-to guide for applying end-to-end security enforcement across a sample Java Web environment. Security concerns covered are authentication, authorization, confidentiality and audit trail. Both declarative and programmatic enforcement controls will be used.More info here: The Anatomy of a Secure Web App
Prerequisites
- Debian or Redhat Linux machine with OpenSSL installed
- Java 8 SDK installed.
- Git installed.
- Apache Maven 3 installed.
- Firefox Web Browser
-
Setup of LDAP server by completing the the Apache Fortress Core Integration Tests in either of these two quickstarts:
Pick One:
- ApacheDS: README-QUICKSTART-APACHEDS sections 2,3 & 4
- OpenLDAP: README-QUICKSTART-SLAPD sections 2 and 3
Demo Installation Instructions
Tutorial installation requires completion of these sections:- Set Hostname Entry
- Managing PKI Keys
- Apache Directory SSL -OR- OpenLDAP SSL
- Apache Fortress Core SSL
- Install MySQL
- Apache Tomcat SSL
- Apache Fortress Demo
Demo Security Architecture Overview
The following block diagram illustrates the layered approach used to enforce security in this tutorial: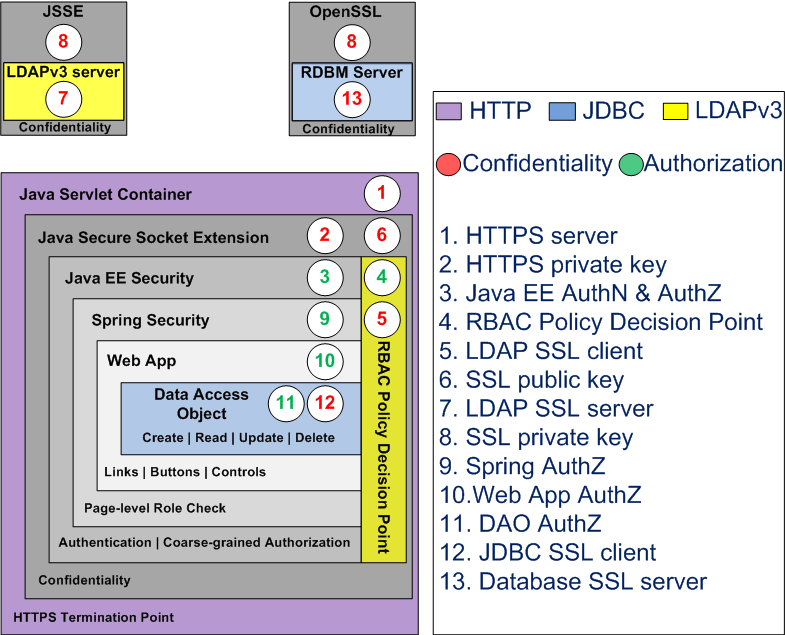
Getting Started - Generating the tutorial's how-to guide
This tutorial uses javadoc that is contained within the apache-fortress-demo web application. To generate, follow these instructions:-
Download and extract bundle:apache-fortress-demo source bundle from GitHub
Or clone:git clone https://github.com/shawnmckinney/apache-fortress-demo.git
- Change directory into the project:
cd apache-fortress-demo
- Set java and maven home
- Build the javadoc for this package:
mvn javadoc:javadoc
- Point your web browser to the javadoc: file:///[apache-fortress-demo]//target/site/apidocs/overview-summary.html.
- Complete the sections under Demo Installation Instructions section
Infrastructure Installed During this Tutorial
Infrastructure Configured During this Tutorial
Security Functions Covered
This sample Web application shows how-to do the following:- Java EE Authentication with UserId and Password
- Java EE Coarse-grained Authorization using Roles
- Spring Coarse-grained Page Authorization using Roles
- Medium-grained Authorization inside Web Framework using RBAC Roles and Permissions
- Fine-grained Authorization inside Data Access Objects using RBAC Permissions
- HTTPS Confidentiality
- LDAP v3 Confidentiality
- JDBC Confidentiality
These concepts apply to other Web application infrastructure configurations. If you find security flaws, or have questions about Apache Fortress, submit to Apache Fortress Discussion list.